Continue reading "10+ Free Shopify Themes for a Sleek, Affordable Design in 2023"
Search Results for: design
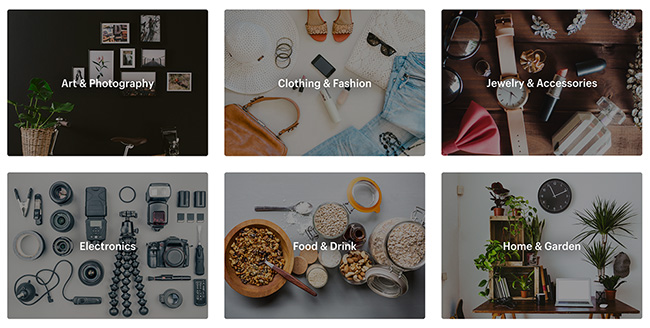
Best WooCommerce Themes for the Perfect Online Store Design (2023)
Articles Ecommerce Resources WordPressAfter that, our testing allowed us to compare the best WooCommerce themes from a more subjective nature. We looked into the overall value of these themes and picked the ones that are most versatile when it comes to design settings and templates.
Continue reading "Best WooCommerce Themes for the Perfect Online Store Design (2023)"
25+ Best Ecommerce Website Designs for Inspiration (2024)
Articles Ecommerce Design Ecommerce WebsitesFor any business that wants to sell online, having a well-designed website is vitally important. Pick up any ecommerce sales or marketing strategy, and the first thing you’ll notice is that they will all talk about the importance of good web design.
As we’ve said before, your website is a digital storefront, and it’s your primary chance to make an impression on visitors.
Continue reading “25+ Best Ecommerce Website Designs for Inspiration (2024)”
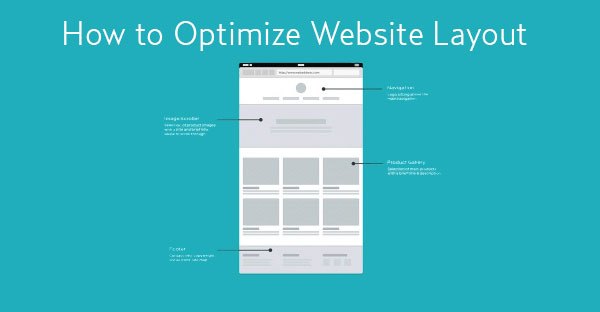
The Best Layout Design Hierarchy for Your Homepage to Grab More Customers and Sales
Ecommerce Selling AdviceLaying out your online store raises various questions. Your homepage serves as a hub for the best stuff on your online store, with components such as image sliders, shopping cart buttons, product thumbnails and buttons, and email marketing subscription forms.
Best Free Software for Designers and Developers for 2024
ArticlesWhen getting ready for the year ahead, it’s a good idea to fill in the gaps in your software collection, especially when there is so much good software you can now get online for free.
Beware however – not all “free” things are really free. First, of course, you should avoid cracked versions of payware, because that can get you into trouble in more ways than one. Another thing to watch for is that some free software is supported by ads, while other software may have undesirable behaviors such as tracking what you do online.
Continue reading “Best Free Software for Designers and Developers for 2024”
Discover the 10 Sources of Inspiration for Designers and Filmmakers
ArticlesCreativity is an enigmatic aspect of human experience; it is often difficult to identify what it is that drives this impulse and the elements that inspire an artist's work.
Written from the perspective of a practicing painter and writer, this post brings together ten areas that are sources for artistic inspiration.
When an individual chooses a career path of freelance art or design, a career that depends on a constant supply of creativity, it is important to recognize what inspires the work, and how to stimulate one's imagination.
Continue reading “Discover the 10 Sources of Inspiration for Designers and Filmmakers”
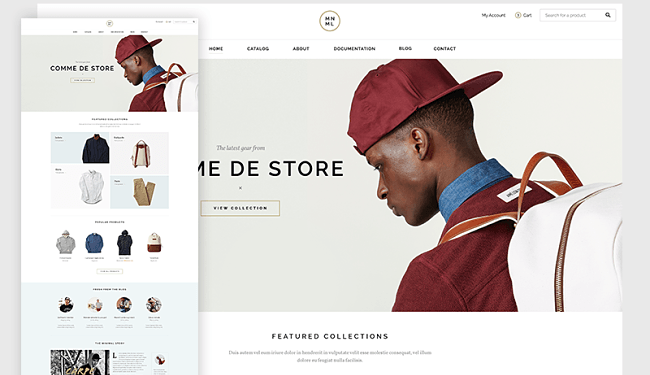
10 Elements That You Should Incorporate Into Your Ecommerce Website Design
Articles EcommerceIn the digital marketplace, the design of your e-commerce store is much more than just a pretty facade; it's a critical component of success.
A well-designed online store does not only captivate visitors but also facilitates a seamless shopping experience, guiding them from initial interest to the final purchase with ease and efficiency.
In this article we delve into the essential design elements that are the backbone of a successful e-commerce website.
Continue reading 10 Elements That You Should Incorporate Into Your Ecommerce Website Design
Top 16 “We Accept Credit Cards” Designs for Your Website
ArticlesYou’ve probably noticed that credit cards are gaining ground, unless, of course, you’ve been on a mission to the moon during the last decade. Not only are they gaining ground, but they are essential in any ecommerce enterprise.
Now that we’ve settled this, it's good to also know that credit cards come in various colors, have several backgrounds, and each has its own special features. Some mightier than others, but all good for commerce. That's why you shouldn't miss to add “We Accept Credit Cards” sign from your online shop.
Continue reading “Top 16 “We Accept Credit Cards” Designs for Your Website”
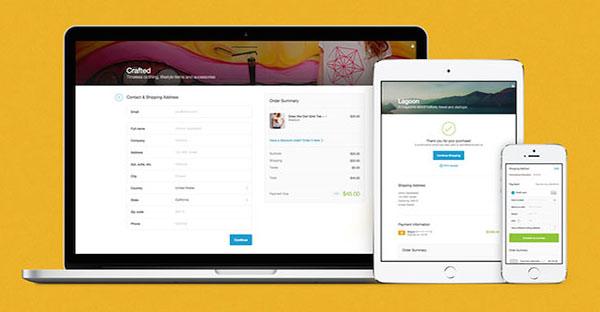
Top 5 Principles for an Improved Checkout Design
Ecommerce Selling AdviceWe have all probably been victims of an impractical or just plain unusable checkout system while trying to perform a purchase online. Most websites are built with the intention to convert the visitors into customers but that won’t happen when a poor checkout design is being put to use. Potential customers are looking for a quick and satisfying online experience which means you need to make sure that happens.
Continue reading “Top 5 Principles for an Improved Checkout Design”
Top 6 Ways to Add Magic to Your Designs with Photoshop
ArticlesWant to add a bit of magic on your graphic designs? Try the following tutorials that will help you inject magical visual effects to your artwork.
Continue reading “Top 6 Ways to Add Magic to Your Designs with Photoshop”